Cyber Risk
Stop Cyberattacks Now with Threat Lifecycle Management
Tackle every facet of today and tomorrow’s threat landscape with guidance from Kroll’s Cyber Risk experts. Enriched by frontline threat intel from 3000+ incident response cases every year, Kroll’s protection, detection, and response solutions immediately mature your cyber posture.
With the attack surface constantly growing in scope and complexity, it is essential to take proactive steps to defend your organization. Enter Kroll’s Threat Lifecycle Management. With our end-to-end cyber risk solutions, we help uncover exposures, validate the effectiveness of your defenses, implement new or updated controls, fine-tune detections and confidently respond to any threat.
Cybersecurity Solutions to Protect, Detect and Respond Against Cyberattacks
Hover over to explore
From system upgrades or a move to the cloud … to applications meant to improve the customer experience … and to integral third-party relationships, one misstep can cascade into IP theft, wire fraud, ransomware, data breaches and more; not to mention regulatory action, civil litigation and reputational damage. That’s why we’ve structured end-to-end solutions to manage the entire threat lifecycle.
What Sets Kroll Apart

Expertise and Bench to Tackle Any Cyber Challenge
600+ elite investigators and hackers handling 3000+ incidents and 100K+ hours of offensive security work means you get expert guidance throughout your entire journey toward cyber resilience.

Frontline Threat Intelligence to Drive Confident Decisions
Centralized platform ingests, enriches, and contextualizes IR case data, OSINT, and behavioral intelligence to accelerate investigations, detection engineering, and optimize testing and simulation exercises.

Complete Response Suite to Tackle the Entire Incident Lifecycle
Incidents can stem from endless sources and carry long tails. With technical and advisory expertise Kroll is uniquely equipped to boost preparedness and minimize impact throughout the entire incident lifecycle.
The True Cyber Risk Retainer
Advance your security posture with a cyber retainer unlike any other. In a constantly evolving threat landscape, the ability to adapt is critical. The Kroll Cyber Risk retainer combines flexibility with prompt access to support from the world’s No. 1 incident response provider.
- Rapid response service levels for peace of mind in the event of an emergency
- Access to an elite, global team of 600+ incident response and breach notification experts
- Customizable for optimal coverage
Kroll Responder: Unrivaled Managed Detection and Response (MDR)
Kroll Responder: Unrivaled Managed Detection and Response (MDR)
Kroll Responder MDR delivers 24/7 security monitoring, earlier insight into threats, and complete response that goes far beyond simple threat containment to understanding the root-cause, hunting for further evidence of compromise and eradication. With frontline threat intelligence from 3,000+ incident response cases a year fueling more accurate, faster services across the threat lifecycle, Kroll Responder is consistently recognized as industry-leading by security sector analysts.
- 360-degree visibility to see and stop hidden threats
- Complimentary $1 million incident protection service warranty with no vendor-specific hardware requirement
- Enriched MDR for Microsoft Security with Kroll Responder MDR for Microsoft
- Kroll Responder named as an MDR sector “Champion”, and recognized as an Overall Leader in MDR
Exposure Management and Validation Capabilities
Exposure Management and Validation Capabilities
Actively reduce your attack surface by identifying previously undiscovered exposures across your digital footprint. Merging threat intelligence directly from the frontlines with extensive digital risk protection capabilities, our ethical hackers and incident responders apply the latest adversary techniques to craft tests, simulations and assessments unique to your environment. This ensures that critical detection and response gaps are addressed and security procedures, policies and controls are up to date. Explore more:
- Digital risk protection
- Penetration testing
- Red Team exercises
- Incident Response Tabletops
KAPE: Expedite and Optimize Forensic Investigations
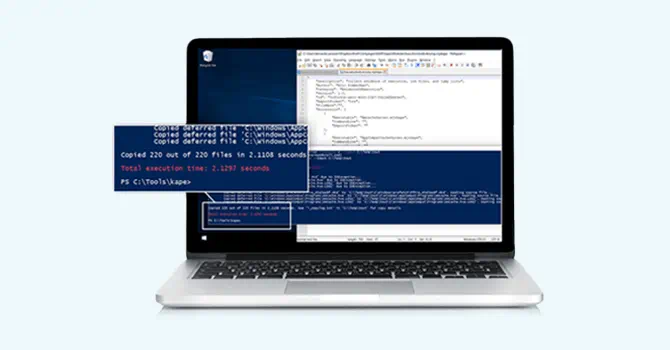
KAPE: Expedite and Optimize Forensic Investigations
Jumpstart your forensic investigations by collecting and processing forensically useful artifacts within minutes with Kroll's Artifact Parser and Extractor (KAPE). KAPE draws directly on our experts’ unique frontline insight from complex cyber incidents and performing digital forensics and evidence collection for thousands of companies.
- Download KAPE
- Purchase a KAPE Enterprise License
- Sign for KAPE training and certification
Join the Kroll Cyber Partner Program and Get Lifetime Returns
|
Strengthen your client relationships and build true resilience with the Kroll Cyber Partner Program. As threats, regulations and technology continue to evolve, you need a security partner capable of delivering end-to-end cyber risk solutions and expertise that can adapt to your clients’ changing priorities. When you become a Kroll Cyber Partner, you benefit from:
|
 Get Started
Get Started |

Strengthen your client relationships and build true resilience with the Kroll Cyber Partner Program. As threats, regulations and technology continue to evolve, you need a security partner capable of delivering end-to-end cyber risk solutions and expertise that can adapt to your clients’ changing priorities. When you become a Kroll Cyber Partner, you benefit from:
- Lifetime account relationships, with long-term commission opportunities
- Over 40 cyber solutions for resale or referral
- $1 million complimentary incident protection warranty
- 600+ experts across 19 countries
Experienced. Trusted. Recognized.
Cyber Security Case Studies
Cyber Security Case Studies
Kroll's elite cyber risk experts deliver end-to-end cyber security services for organizations in a wide range of sectors, across the globe.
Learn how Kroll employed its comprehensive knowledge of Cyber Security Services, Financial Fraud, Workflow Assessment, and Physical Security Services to resolve and enable a fast recovery from the damage caused by a highly complex security breach.
Discover our full range of cyber security case studies below.
Data Breach Outlook: Finance Surpasses Healthcare as Most Breached Industry in 2023
Data Breach Outlook: Finance Surpasses Healthcare as Most Breached Industry in 2023
In 2023 finance was the most breached industry, accounting for 27% of the breaches handled by Kroll, compared to 19% in 2022. Supply-chain risk was a constant menace, driven by the MOVEit Transfer vulnerability and a rise in social engineering.
Read our Data Breach Outlook report for more insights.
Frequently Asked Questions
Talk to a Kroll Expert
Connect With Us








Cyber Governance and Strategy
Manage cyber risk and information security governance issues with Kroll’s defensible cyber security strategy framework.
Threat Exposure and Validation
Proactively identify your highest-risk exposures and address key gaps in your security posture. As the No. 1 Incident Response provider, Kroll leverages frontline intelligence from 3000+ IR cases a year with adversary intel from deep and dark web sources to discover unknown exposures and validate defenses.
Incident Response and Litigation Support
Kroll’s elite security leaders deliver rapid responses for over 3,000 incidents per year and have the resources and expertise to support the entire incident lifecycle.
Notification, Call Centers and Monitoring
Kroll’s data breach notification, call centers and monitoring team brings global breach response expertise to efficiently manage regulatory and reputational needs.
Managed Security Services
World-renowned cyber investigators and leading technology fuel Kroll’s managed security services, augmenting security operations centres and incident response capabilities.
Kroll Cyber Partner Program
The only cybersecurity partner program to deliver lifetime returns to partners.
Cyber
Kroll at RSA Conference 2024
Join Kroll experts at the RSA Conference in San Francisco May 6-9, 2024. Stop by booth 2239 in the South Expo Hall to meet our team.

Threat Intelligence
Q1 2024 Cyber Threat Landscape Virtual Briefing
Join the Q1 2024 Cyber Threat Landscape Virtual Briefing as Kroll’s cyber threat analysts outline notable trends and insights from our incident response intelligence.

Enterprise Risk
Kroll to Exhibit at RISKWORLD Conference 2024
Kroll is pleased to announce that it will be exhibiting at the RISKWORLD 2024 conference from May 6–8, 2024 in San Diego.

Press Release
Kroll named as Major Player in IDC’s Worldwide Cybersecurity Consulting Services 2024 Vendor Assessment

Press Release
Kroll Appoints Dave Burg as Global Head of Cyber Risk to Bolster World-Leading Business

Press Release
Kroll Expands Cyber Partner Program with MSP Specialization

Press Release
Kroll Responder Named as Overall Leader in The KuppingerCole Leadership Compass for Managed Detection and Response Services