Automate Threat Modeling to Mitigate Cyber Risks at Scale
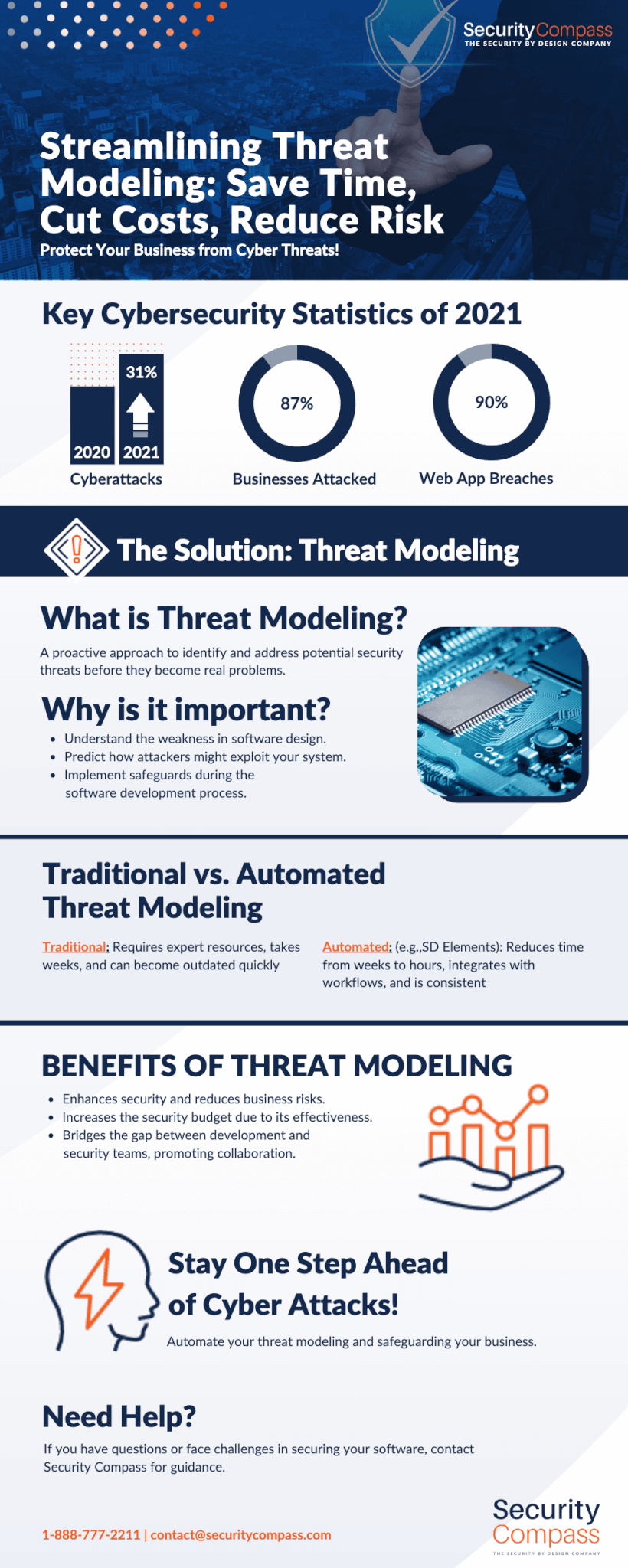
Cyberattacks on organizations continue to increase. According to Accenture’s State of Cybersecurity Resilience 2021 Report, the average company faced 270 attacks in 2021, an increase of 31 percent over 2020.
These attacks lead to business disruptions, stolen data, ransomware, financial losses, and damaged reputations. Gartner® reports that “87 percent of organizations know that they’ve suffered an attack” and “65 percent of organizations surveyed reported attacks disrupted their businesses through “crippled systems” and/or resulted in “data spillage”.1
The threat of cyberattacks is increasingly seen as a Board-level issue for which organizations are ill-prepared. The EY Global Board Risk Survey reported that 84 percent of Boards do not believe their organizations have a highly effective risk management strategy. Gartner® cites “Boards identify cybersecurity risk as the Boards’ second highest source of risk for the enterprise.”1
Attacks are Targeting Applications
So how are criminals successfully breaking into enterprise systems? The 2021 Verizon Data Breach Investigations Report cited web applications as the attack vector in over 90 percent of the data breaches researched. The Forrester State of Application Security 2021 report is more succinct, stating “web applications are the most common form of external attack.”
Changes in how organizations build software require a shift in strategy for security and development teams.
Faster time-to-market can challenge security
Web applications are publicly facing, making them easy to find so this attack vector is not surprising. The data these applications manage, including customers’ personal information, is frequently the target of the attack. Rapid development methodologies like Agile, DevOps, and Continuous Integration/Continuous Delivery (CI/CD) mean development teams are building and deploying new software faster than ever, often at the expense of security.
Insecure design hits the OWASP Top 10
The Open Web Application Security Project (OWASP) publishes a Top 10 list of the most critical web application security risks. The 2021 version added “Insecure Design” as a new category. It focuses on risks relating to design and architectural flaws or “missing or ineffective control design” in software and calls for more use of threat modeling, among other things, in pre-code activities.
Cloud Deployments Require New Strategies
As teams adopt cloud strategies, they often fail to recognize the different controls required in the new deployment environment. Avoidable “Security Misconfigurations” are also cited in the OWASP Top 10. This includes missing appropriate cloud security hardening and incorrect security settings in the application frameworks and servers, and the use of default accounts and passwords.
Security Testing is Reactive
Using scanning tools like static and dynamic analysis to test for security issues is common. For most software projects, a functional specification is generated, architects provide a design to development, and code is produced. Once coding begins, various security testing tools can be used to identify errors that could result in vulnerabilities. Late in the development lifecycle, penetration testing and dynamic analysis can augment other testing methodologies.
This process is reactive: it relies solely on test results to identify security issues after they have been produced. Fixing these vulnerabilities later in the development process results in higher remediation costs and delays in releases.
Threat Modeling Anticipates Weaknesses
Security testing is not enough. More mature organizations also focus on prevention. Threat modeling helps identify and avoid security issues proactively. A good threat model enumerates the weaknesses inherent to the frameworks used in the application and the deployment environment. It anticipates how an attacker would exploit an application or system and specifies security controls from an organization’s secure coding standards to mitigate the risk from each threat. These controls then become part of the application’s specifications; they are assigned to development and included in test cases to validate that all specifications are met.
By anticipating threats and ensuring controls are implemented during the development process, threat modeling reduces the number of findings when security testing begins which, in turn, reduces remediation time.
Threat Modeling and Security Standards
Building more secure software requires anticipating how the design and execution of an application can introduce weaknesses, then implementing controls during the development process to mitigate risk. Development and security teams can do this through threat modeling. As the benefits of threat modeling have been embraced by security teams, a number of industry and government organizations are promoting more widespread adoption and offering guidelines.
- In 2021, the National Institute of Standards and Technology’s (NIST) published Recommended Minimum Standard for Vendor or Developer Verification of Code in response to the U.S. President’s Executive Order (EO) on “Improving the Nation’s Cybersecurity (14028)”. It lists threat modeling as the first of six recommended techniques for verification of code by developers.
- Prior to this, NIST issued guidelines on Mitigating the Risk of Software Vulnerabilities by Adopting a Secure Software Development Framework (SSDF). It recommends threat modeling to help “Design Software to Meet Security Requirements and Mitigate Security Risks.”
- The US Department of Defense Enterprise DevSecOps Reference Design cites the use of a threat modeling tool to “Document system security design, analyze the design for potential security issues, review and analysis against common attack patterns, and suggest and manage mitigation.”
- NIST Special Publication 800-161 1 – Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations in SA-15(8) calls for the reuse of threat and vulnerability information identified through “threat modeling and vulnerability analyses from similar systems, components, or services to inform the current development process.”
- Draft NIST Special Publication 800-218 – Secure Software Development Framework (SSDF) Version 1.1: 3, Recommendations for Mitigating the Risk of Software 4 Vulnerabilities requires organizations to “Use forms of risk modeling, such as threat modeling, attack modeling, or attack surface mapping, to help assess the security risk for the software.”
What’s Next?
Threat modeling allows organizations to identify insecure designs and anticipate security weaknesses in applications before the applications or functionality are built. The result? Secure software can be deployed nearly as fast as if it were being built without security or compliance in mind.
Some organizations have been hesitant to adopt threat modeling, perhaps due to the pains leaders and practitioners may have experienced, witnessed, or heard about manual threat modeling approaches. The standards and guidelines cited above are among the significant signs that lead us to believe the industry – software producers and consumers in the private and public sectors – will demand greater cybersecurity protection. This requires creating or maturing threat modeling programs.
Threat Modeling Fosters a More Mature Security Culture
In many organizations, implementing threat modeling kicks off a virtuous cycle to further improve the security of the enterprise. By anticipating threats and building security mitigation controls into the normal development process, rework is reduced. This in turn reduces friction between security and development.
Further, our research shows that organizations that implement threat modeling see an increase in their security budget. The threat modeling process illustrates exactly why security controls are required, which provides evidence of the risks inherent in and to different environments and processes, and how security tooling can mitigate those risks.
“The more visibility we’ve been able to provide to our leadership, the more interested they are in offering improvement. I do think a lot of that does come from starting at the end of the design phase.“
Director of Cybersecurity Architecture in a Financial Services Company
Scalable Threat Modeling
Traditional threat modeling requires scarce security resources and senior development personnel to map data flows, diagram attack trees, prioritize threats, and recommend mitigation controls. It can take weeks and quickly become out of date as customer demands change. Its effectiveness and consistency are subject to the skills and experience of the threat modeling team.
As organizations seek to accelerate product innovation and delight customers, a different approach is needed to modeling software risk that tightly integrates with product workflows and empowers product teams to deliver secure products at high velocity.
SD Elements from Security Compass automates threat modeling, reducing the time required from weeks to hours. After the completion of a project survey, SD Elements identifies weaknesses that threats target and enables the delivery of mitigation controls directly to those responsible in development, security, and operations. By anticipating threats and building mitigations as part of the normal development process, security testing is simplified, more proactively, and easily scaled across an entire software portfolio.