It happens all the time — weekly, if not daily.
A customer approaches us and tells us that part of their mandate is to ensure their development teams are trained and able to protect against security vulnerabilities. Their budget, however, is either minimal or controlled by another department in their organization.
With application security gaining more and more visibility worldwide, we continue to ignore the importance of building a culture of security from the foundational level. How can we expect our development teams to “just know” when we aren’t providing them with the tools necessary to do their jobs?
Securing a budget for training can be difficult. Many times, it involves multiple people across multiple departments with widely varying opinions. The more red tape, the harder it is to gain buy-in for security awareness training.
We have witnessed first hand the benefits of proactive rather than reactive training. Here are some tips on how to persuade and secure funding for something that is increasingly becoming more vital to your organization’s success.
Use facts to secure budget for security awareness training
Proactive training has a lower cost than reactive recovery. We’ve all heard the saying, “do it right the first time,” and when it comes to developing secure applications, this holds extra true.
According to WhiteHat Security, the average website has 23 vulnerabilities, 13 of which are serious, and 48 percent of which will eventually get remediated. The average time it takes to remediate these vulnerabilities is 200 days. Needless to say, if training can help development teams eliminate vulnerabilities from the start, the whole organization will save a lot of time, headaches, and ultimately money.
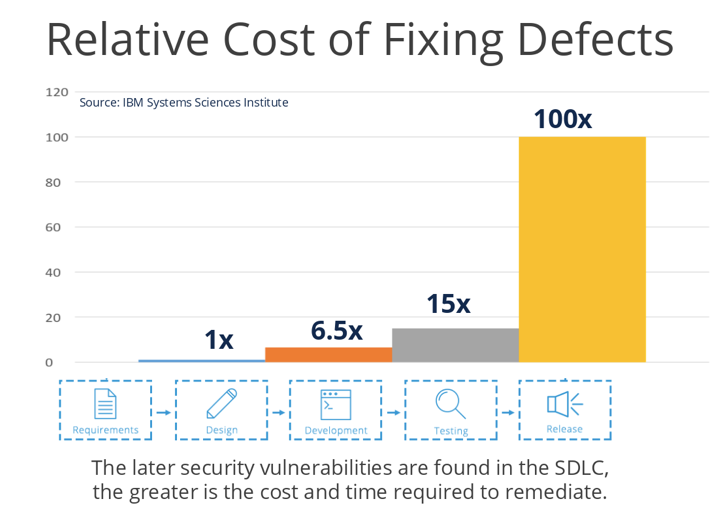
If you’re fighting for a larger training budget, you can argue that you are saving your organization money by training your developers to avoid potential security risks. The table below by IBM shows that it is 100 times more expensive to fix a defect after it has been released than during the design phase.
Build security training into your development process
Making training an integral part of your SDLC can help ensure that training isn’t treated like an afterthought or an add-on. When building your strategy, training should come from the top down and should (in the best case scenario) be mandatory. It may seem harsh to force training on your team, but eventually, you’ll build a security culture where employees want to learn so that they don’t get left behind.
Without the proper training, everything becomes a reactive game of trial and error. It’s important to learn the basics, and then employ them on a larger scale. Everyone needs to have a baseline of fundamental knowledge. If we rely on humans to build applications, we are at the risk of errors. If you build training into your overall plan the cost of training becomes a fraction of the cost of remediation.
Security training can help with employee retention
Developers in the tech world today have boundless opportunities. There are a lot of good jobs, and developers regularly receive a lot of enticing offers with a lot of potential benefits. They tend not to stay too long in one place because there are always “better” opportunities elsewhere. Churn is expensive and carries a significant risk for your organization.
Organizations that provide training and growth opportunities see less turnover. In a recent survey of millenials on the job market, a whopping 53 percent of respondents cited “learning new things or having access to learning or professional development opportunities” as a reason they would consider staying in one position longer.
Investing in your team saves you the cost of replacement and re-training.
Make security training continuous and tailored
Nobody wants to waste time. The most frequent argument that we hear against training, and that anyone is likely to hear in their own organization, is that development teams “don’t have time” for training.
Some major time savers are to ensure that your teams take only the training they require and that they are continuously reminded of what they’ve learned. If they invest the time into the training, ensure that your organization is calling to attention the importance of what they have learned, and how it is improving the business.
Continuous, tailored learning increases retention and buy-in, which will lower the amount of remediation in the end. Role-based learning that benefits both the organization and the student will be seen as the most valuable and thus provide the highest adoption rates.
In the end, the thing to emphasize is that developers will have more time for more important and enjoyable work if they are trained in ways to avoid vulnerabilities that will require lengthy remediation later. On a higher level, this means employees are focusing on their core strengths which ensures faster releases and time to market.
About Security Compass
Security Compass, a leading provider of cybersecurity solutions, enables organizations to shift left and build secure applications by design, integrated directly with existing DevSecOps tools and workflows. Its flagship product, SD Elements, allows organizations to balance the need to accelerate software time-to-market while managing risk by automating significant portions of proactive manual processes for security and compliance. SD Elements is the world’s first Balanced Development Automation platform. Security Compass is the trusted solution provider to leading financial and technology organizations, the U.S. Department of Defense, government agencies, and renowned global brands across multiple industries. The company is headquartered in Toronto, with offices in the U.S. and India. For more information, please visit https://www.securitycompass.com/








