The US federal government has long been concerned with the security of its software and systems and those of organizations — with good reason. Operation Aurora, in 2009-10, targeted and stole design documents and source code from over 40 technology companies, including Northrop Grumman, Adobe and Cisco. The 2013 APT1 attacks victimized over 140 organizations.
Nation-state attacks on government agencies and critical infrastructure continue to pose a significant threat. More recent examples include:
- A 2020 attack by Russian hackers compromised the code base of SolarWinds’ Orion IT monitoring system, successfully adding a backdoor. A subsequent software update by SolarWinds distributed the compromised application to over 18,000 customers, including the US Departments of Defense, Energy, Commerce, State, Homeland Security, Treasury, and Justice.
- In 2019 researchers identified a backdoor in Chinese-made security cameras that captured and sent back to China data from a Fortune 500 company. State, local, and federal government organizations also used the camera and were subject to the same backdoor.
- A 2015 breach of the US Government’s Office of Personnel Management (OPM) by Chinese actors exposed highly sensitive questionnaires used for background checks and security clearances on over 20 million people, including fingerprints.
A Brief History of Federal Security Standards and Authority to Operate
The federal government stepped up efforts to improve the security of the software and systems it developed and used in the early 1990’s with the DoD Information Technology Security Certification and Accreditation Process (DITSCAP). DITSCAP provided a structured approach for identifying, assessing, and mitigating security risks for information systems. This coincided with efforts to standardize the “Authority to Operate” (ATO) process. ATO is a formal authorization provided by a designated approving authority (DAA) that allows an information system to operate in a production environment. In short, one must have ATO authorization to provide software and systems to the federal government.
In 2005, the DoD replaced DITSCAP with the DoD Information Assurance Certification and Accreditation Process (DIACAP). Attaining ATO under DIACAP required compliance with guidelines for securing information systems published in NIST SP 800-37: Risk Management Framework for Information Systems and Organizations. In 2010, to address the unique risks introduced by the growth of cloud services, the General Services Administration (GSA), the Department of Homeland Security (DHS), and the National Institute of Standards and Technology (NIST) launched the Federal Risk and Authorization Management Program (FedRAMP). It is mandatory for all federal agencies to use FedRAMP-authorized cloud services.
DIACAP was used until 2014 when it was replaced by the newer NIST Risk Management Framework (RMF) detailed in SP 800-53: Security and Privacy Controls for Information Systems and Organizations. Achieving ATO or FedRAMP now requires compliance with the security controls detailed in SP 800-53 and SP 800-53A.
eMASS, ATO, and FedRAMP
As noted, agencies and vendors must meet the security requirements of the RMF to achieve ATO or FedRAMP accreditation. Rapidly developing and deploying secure software in a way that meets ATO requirements, especially within environments where software project volume, complexity, and delivery pace is high, and security expertise is in short supply, makes attaining ATO or maintaining continuous ATO (cATO) extremely difficult.
Further, tracking evidence of compliance with hundreds of security controls using spreadsheets and documents for a single application is subject to error. Scaling a manual process to thousands of systems and requiring ATO And FedRAMP accreditation is inefficient at best. For agencies and vendors working toward accreditation, manual processes are time consuming and delay accreditation.
To streamline the ATO And FedRAMP process, in 2010 the DoD introduced the Enterprise Mission Assurance Support Service (eMASS). eMASS is a web-based platform providing a centralized and standardized method for managing and tracking security requirements and controls for federal systems across the RMF life cycle. It maps to requirements detailed in SP 800-53, the Federal Information Security Modernization Act (FISMA), and other federal standards.
How SD Elements Helps
The NIST RMF requires organizations to identify risks and assign appropriate controls. Doing so manually is subject to inconsistent assessments of risk and assignment on controls. Tracking the status of each using spreadsheets or shared documents is prone to error and presents auditability challenges.
SD Elements automates this process through a centralized platform, assisting across the RMF to ensure compliance, including:
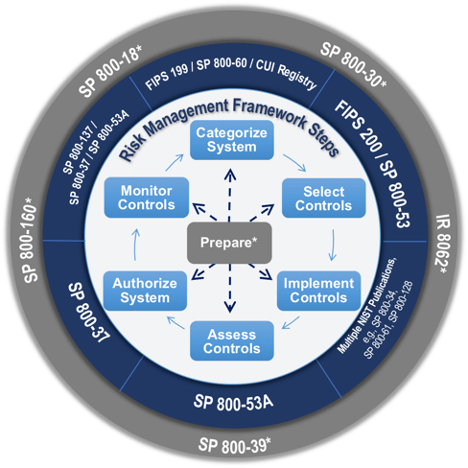
Select Controls: After completing a short survey of the applications technical stack, deployment environment, and applicable standards, SD Elements produces a complete list of security controls mapped to the RMF, including SP 800-53 and SP 800-53A .
Implement Controls: SD Elements translates the identified controls into actionable tasks and delivered directly to the development, security, and operations personnel responsible for their implementation through their existing workflow tools.
Assess Controls: SD Elements also provides test plans for validating each control and provides on-demand tracking of the status of each control. Finally, SD Elements works with eMASS, allowing exporting of compliance reporting against NIST controls to eMASS.
Next Steps
SD Elements is an important tool for building secure software. By anticipating threats and ensuring development, security, and operations implement NIST-required controls during the development process, it reduces the number of findings ATO and FedRAMP accreditation begins.
Assessors working with SD Elements and eMASS are now able to see a complete picture of how software was built from the beginning of the development lifecycle, enabling more rapid assessment for ATO and FedRAMP.
eMASS and SD Elements are powerful tools that are essential components of any government organization’s cybersecurity strategy. eMASS and SD Elements work together to define, track, and manage good cybersecurity practices. By providing a comprehensive and customizable solution for managing security and compliance, these systems help to improve security, streamline processes, and reduce costs.
You can learn more about how SD Elements supports government customers and accelerates ATO accreditation here.









