Simplify Threat Modeling with Enhancements to SD Elements Threat Modeling Diagrams, Reusable Components, and Advanced Reporting Capabilities
Software threat modeling is a foundational requirement for ensuring secure software development. However, many organizations today still struggle to effectively model software applications. Application security experts, who have traditionally led threat modeling exercises, are in short supply. Software developers are now being asked to add threat modeling to their skill set. However, most software developers are not threat modeling experts. Asking developers to take on an additional and vital task can impact hitting their release deadlines.
Identifying and mitigating software threats prior to software release is required by the vast majority of organizations that develop software. For example, according to a recent study, 2022 Developer Perspectives on Application Security, 76% of software developers report that their applications cannot be released until threats of specified authority are mitigated. 65% report that addressing threats from the security team is required. To help developers succeed, a better, more developer-centric approach to threat modeling is required.
In response to this need, Security Compass has developed SD Elements, a developer-centric software threat modeling tool, to help software teams take an automated approach to threat modeling at the very beginning of their development cycle — without requiring the expertise of a security expert. With the release of SD Elements 2022.4, we are making threat modeling easier than ever before for application security and development teams. New features now available in SD Elements 2022.4 include the ability to:
- Generate accurate threat models and collaborate on their application’s design and data flow
- Reuse existing components along with their identified threats and countermeasures across projects
- Reduce the level of expertise needed to generate reports
- Integrate with Snyk Open Source Software Composition Analysis (SCA)
- Customize SD Elements security content
New and updated security content, just-in-time training modules, and eLearning courses demonstrate Security Compass’ commitment to ensuring software developers have the training and knowledge required to effectively protect their organizations from emerging and existing application security threats.
These new capabilities in SD Elements help software development and application security teams:
- Improve collaboration between security, software development, hardware engineering, and DevOps teams
- Improve developer productivity
- Obtain visibility into the security and compliance state of software across an organization’s entire software portfolio
- Reduce time and costs associated with demonstrating compliance with multiple security standards and regulations
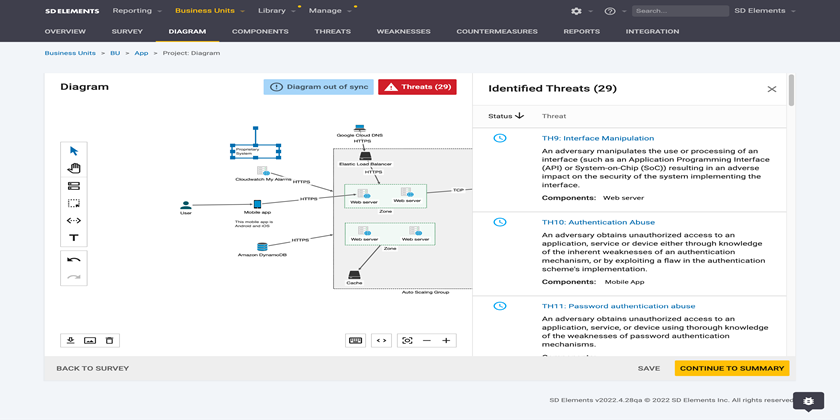
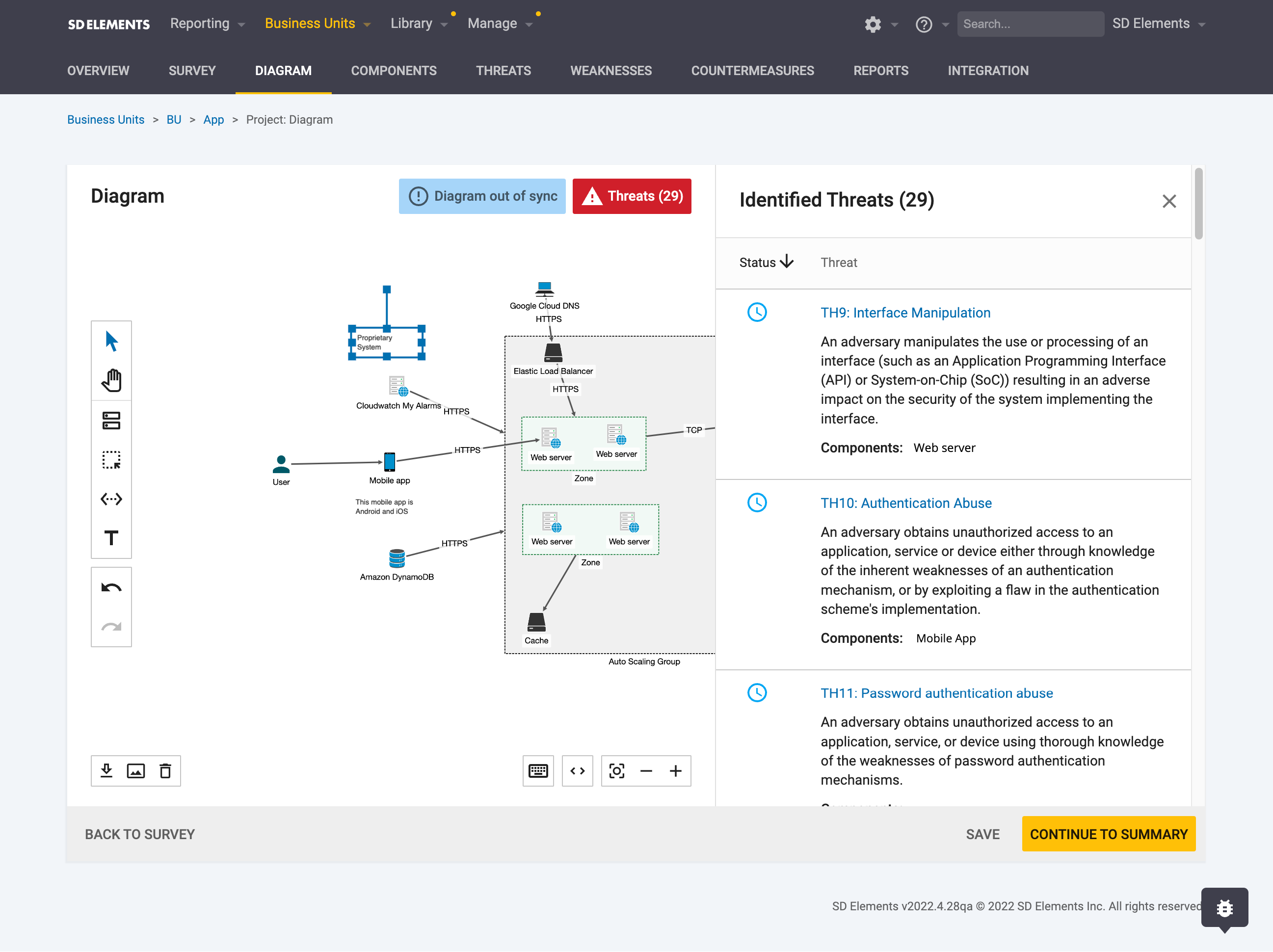
Updated Threat Model Diagrams
Threat modeling is a foundational exercise in delivering secure software applications. But, in order for threat modeling to be viewed as a value add activity by both application security and software development teams, generated threat model diagrams must accurately display the application architecture, including zones and nested zones. Threat model diagrams should also include the ability to add notes to the diagram. Application security and software development teams, using the threat model diagrams, need the context to fully understand the system architecture, threats, and required countermeasures to implement and effectively collaborate to help ensure the security of the software.
Updates to threat model diagrams in the 2022.4 release (see 2023.3 release) include the ability to nest zones and add diagram notes. These new features further enhance the threat modeling experience for application security professionals and developers. After generating a threat model, zones can be nested to ensure the diagram matches the organization’s architecture. Diagram notes allow development and application security teams to represent their software application’s design and data flows quickly and easily, as well as add any important notes to the threat model diagram to provide additional context.
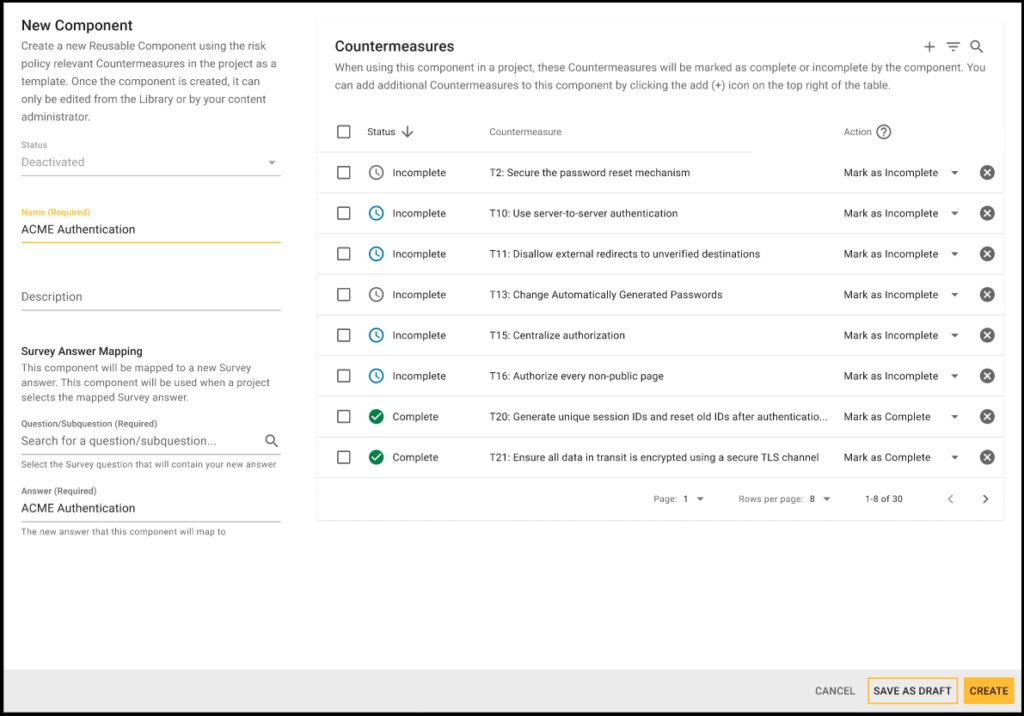
Reusable Components Enhancements
“When developers perform a threat model, they begin to recognize what can go wrong in a system. It also allows them to pinpoint design and implementation issues that require mitigation, whether it is early in or throughout the lifetime of the system.” (Threat Modeling Manifesto)
Over time, patterns will reoccur within systems and software, i.e. recurring threats, weaknesses, and their necessary countermeasures. Application security professionals and developers need to be able to reuse these patterns across projects to simplify threat modeling. In prior versions of SD Elements, the process of reusing security patterns found in existing components was manual. Components needed to be manually created in the component library and configured by selecting the appropriate countermeasures.
The latest update to SD Elements reusable components allows application security and development teams to be able reuse existing components’ along with their security patterns, identified threats, and countermeasures across projects. This improves efficiency between security and development teams by leveraging patterns that have already been identified and addressed in other projects. Now, teams can focus their attention on only what needs to be done. When a component is created, it is added to the component library. And once it has been activated by an SD Elements administrator, the component along with the identified threats and appropriate countermeasures are available to every project in the organization.
Advanced Reporting Enhancements
Prior to the 2022.4 release, SD Elements required a high level of SQL expertise to pull data and generate reports. The majority of stakeholders that work in SD Elements do not possess this skill, which created an over-reliance on SD Elements administrators to generate reports.
Updates to advanced reporting in SD Elements 2022.4 create a much more scalable, secure way to generate reports. New contextual reporting capabilities reduce the level of expertise needed to retrieve, combine, and visualize data, as well as create rich reports. A user can simply choose the type of context their task is based on, and then the appropriate and relevant data points are available for selection.
New Snyk Open Source Integration
The use of open source code plays an integral role in minimizing the time spent and cost building out applications. Gartner estimates that 90% of organizations rely on open source code in their applications today. Open source projects may seem fully secure, given that they are maintained by a community, but that is not true. Gartner estimates that more than 70% of applications contain flaws stemming from the use of open source code. Given the widespread use of open source code, the need for software composition analysis (SCA) tools is vital in releasing secure applications.
To address the growing need for SCA tools, SD Elements now integrates with Snyk Open Source (SCA). Snyk Open Source helps minimize open source and other third-party software risks by simplifying security control validation for application security and software development teams. Organizations can now import Snyk Open Source scans to SD Elements. This allows organizations to automatically map their findings to the appropriate tasks in SD Elements and highlight open source weaknesses and required countermeasures to implement. To learn more about SD Elements 35+ integrations, covering application security software, DevOps tools, infrastructure, and issue trackers, visit the SD Elements Integrations page
New Custom Task Mapping
In prior versions of SD Elements, customers were unable to perform custom task mapping. SD Elements verification tools, i.e. SCA, were all built with a default mapping file that connected an organization’s scan results findings to the appropriate countermeasure. By not providing customers with the ability to customize their task mapping, within SD Elements, to their verification tools, led to them manually customizing mapping, which was time-consuming. The other alternative was for customers to rely on the SD Elements integrations team.
With the new custom task mapping feature now available in SD Elements 2022.4, organizations have the flexibility to overwrite default task mappings to customize SD Elements’ security content to meet their needs. Application security and development teams can append their own security content and even change different attributes in their files, such as confidence levels between scan findings to SD Elements.
New Security Content
SD Elements 2022.4 now provides the following security content library updates:
- Azure Kubernetes Services (AKS): New recommended security controls and guidelines help software developers and DevOps teams better secure AKS clusters
- AWS Services: In addition to the existing coverage of AWS’ infrastructure provisioning services, the SD Elements Content Library now supports the following AWS Services: API Gateway, AWS Cognito, AWS Kinesis, Amazon Kinesis Data Firehose, and AWS Web Application Firewall (WAF)
- Payment Card Industry Data Security Standard (PCI DSS): New content is now available for the latest version of PCI DSS, v4.0. This includes a compliance report that maps the “Requirements and Testing Procedures” specified in PCI DSS v4.0 to SD Elements tasks and activities. Organizations that process card holder data can now use this report to identify gaps and/or demonstrate compliance with the PCI DSS standard.
- New security content is also available for the .NET 6 framework, TypeScript, and Android 12 and 13.
Just-in-time-training (JITT) Updates
New just-in-time training micromodules have been added in SD Elements 2022.4 for Ansible (IaC) and key updates for .NET 6 and Secure Software Requirements. For a complete list of the 800+ JITT micromodules now available within SD Elements, please see Security Compass’ Training Curriculum. (If you are a current SD Elements customer, but do not currently have a JITT subscription and would like to learn more, please contact Customer Success or Book a Demo.)
New eLearning Courses
The following Security Compass eLearning courses are now available:
- Ansible – Infrastructure as Code (IaC)
- .NET 6
- Secure Software Requirements
To learn more about these new courses, as well as the more than 40+ other eLearning courses covering application security, operational security, and compliance fundamental and best practices, visit the eLearning Solutions page.
Learn More
The new SD Elements 2022.4 release helps organizations who develop software save time and money and reduce cyber risks by taking an automated, developer-centric approach to software threat modeling, secure development, and compliance. This approach enables software developers and security teams to:
- Continuously model threats at scale
- Proactively write code that significantly reduces risks and remediation costs
- Demonstrate compliance with secure software development standards more easily
- Accelerate software time to market
If you are a current SD Elements customer, please reach out to your Customer Success Manager to learn more.
If you are new to SD Elements, request a demo to learn more.