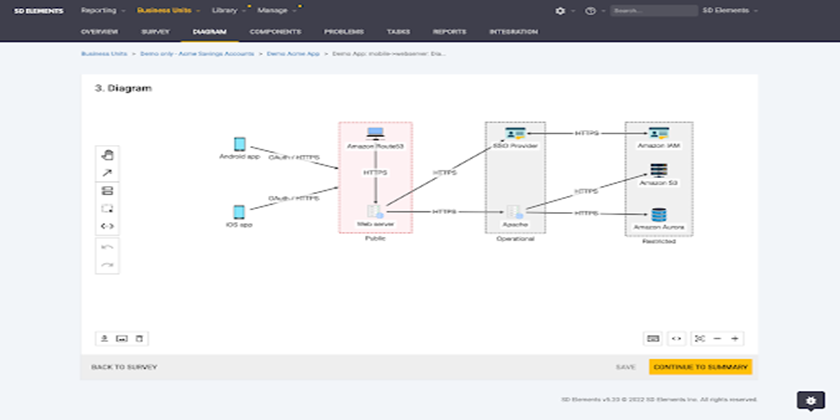
12 Essential Threat Modeling Tools for Enhancing Your Cybersecurity Posture
Welcome to “The Ultimate Guide to Threat Modeling Tools,” your comprehensive resource for understanding the critical role of automated threat modeling in cybersecurity and navigating […]
Read More →